Use a vpn on your work computer the dos donts and why it matters
Use a vpn on your work computer the dos donts and why it matters is a timely topic for anyone who wants to protect privacy, stay compliant, and keep work networks secure without killing productivity. Here’s a practical, in-depth guide that blends real-world tips with solid data, designed for viewers who want actionable steps they can take today. If you’re new to this, you’ll find a friendly, no-nonsense guide that explains what to do, what to avoid, and why it all matters—with real-life examples, checklists, and stats you can rely on.
Introduction: a quick start guide to using a vpn on your work computer the dos donts and why it matters
- Quick fact: Nearly 60% of remote workers report using some form of VPN for work-related tasks, but not all VPN use is created equal, and missteps can cost you security and compliance.
- The core idea: A VPN on your work computer can protect sensitive data, help you bypass geo-restrictions for legitimate business needs, and reduce the risk of on-the-go network snooping—if you use it correctly.
- What you’ll learn in this guide:
- When you should use a VPN at work and when you shouldn’t
- The dos and donts of VPN use on corporate devices
- How to choose a VPN that fits business needs
- Common pitfalls and how to avoid them
- Practical setup steps, best practices, and monitoring tips
- What to watch for in a VPN: encryption standards, logging policies, speed, compatibility with corporate tools, and vendor trust.
- A few handy resources unlinked here for readability: NordVPN, ExpressVPN, Cisco AnyConnect, Palo Alto GlobalProtect, OpenVPN project pages, EFF on VPNs, and best-practices guides from major cybersecurity firms.
Useful URLs and Resources text only Apple Website - apple.com Artificial Intelligence Wikipedia - en.wikipedia.org/wiki/Artificial_intelligence OpenVPN Documentation - openvpn.net Cisco AnyConnect - cisco.com/c/en/us/products/security/vpn-ssl-vpn Palo Alto GlobalProtect - paloaltonetworks.com/products/globalprotect EFF VPN Guide - eff.org/issues/vpn NordVPN - nordvpn.com ExpressVPN - expressvpn.com
Why a vpn on your work computer matters: the big picture
- Privacy vs. policy: A VPN can shield your personal data from insecure networks, but your employer may have policies about monitoring, data access, and approved software. Knowing the rules protects you and your company.
- Security basics: VPNs encrypt traffic between your device and the VPN server, which helps protect against passive eavesdropping on public Wi‑Fi and unsecured networks—especially important when you travel or work from coffee shops, airports, or hotels.
- Compliance and risk: Some industries require strict data handling HIPAA, GDPR, PCI-DSS. A VPN is a tool in the toolbox, but it won’t fix missing encryption elsewhere or weak endpoint security.
- Productivity and access: A well-configured VPN can give you secure access to internal apps, intranets, and databases while you’re away from the office. It can also help you bypass geo-blocks for legitimate research tasks, training, or collaboration with teams in other regions.
The dos of using a vpn on your work computer
- Do check company policy first
- Before enabling or installing any VPN on a work device, review your employer’s IT policies. Some companies require IT-approved clients, mDOTs, or controlled software whitelists. If you’re unsure, ask your IT department or supervisor to avoid policy violations.
- Do use a sanctioned VPN client
- Use the VPN client your IT team recommends. This ensures compatibility with corporate networks, proper DNS handling, split-tunneling rules if allowed, and centralized logging for incident response.
- If your company provides a managed VPN, don’t substitute it with a consumer-grade option. Managed solutions are designed to integrate with authentication systems and security controls.
- Do enable strong encryption
- Choose VPNs with at least AES-256 encryption and robust authentication methods e.g., TLS 1.2+, modern cipher suites. Encryption strength matters more on unsecured networks.
- Do verify DNS and leak protections
- Ensure the VPN blocks DNS leaks and that your real IP isn’t exposed if the VPN connection drops. DNS leak protection reduces the risk of data exposure on public or semi-secure networks.
- Do use two-factor authentication 2FA
- If your VPN supports 2FA, enable it. This adds a critical layer of defense beyond password protection, especially for remote access to sensitive systems.
- Do monitor connection health and logs as appropriate
- Many organizations log VPN activity for security and auditing. Rely on IT guidance for monitoring and avoid accessing or attempting to modify logs yourself.
- Do keep software up to date
- Update the VPN client and the operating system regularly. Patches often fix critical vulnerabilities that could be exploited on corporate networks.
- Do test on non-critical devices first
- If you’re experimenting with a VPN setup, test on a spare or non-production device to avoid disrupting business-critical work.
- Do use secure authentication methods
- Use certificate-based or hardware-backed credentials when available, instead of simple passwords. This reduces credential theft risk.
- Do plan for offline work
- Have a plan if the VPN is down. For example, know the approved downtime procedures, optional access methods, or offline workarounds vetted by IT.
The donts of using a vpn on your work computer
- Don’t bypass IT controls
- Don’t install unauthorized VPNs or client software, disable security features, or tamper with encryption settings. This can create backdoors and violate policy, risking disciplinary action or legal issues.
- Don’t rely on consumer VPNs for work
- Free or low-cost consumer VPNs may not meet enterprise security requirements, can log user data, or leak DNS, which can be a big red flag for compliance.
- Don’t use a VPN for non-work personal traffic on a company device
- Personal usage on a work device can blur privacy boundaries and violate acceptable-use policies. When in doubt, keep personal tasks off the corporate device or use a personal device with a separate network.
- Don’t ignore split tunneling rules
- If your organization disallows split tunneling, don’t force traffic to bypass the VPN for certain apps or sites. This could expose data and violate policy.
- Don’t ignore device ownership and data ownership boundaries
- If you’re using a work device, your employer may have rights to monitor, manage, or wipe data. Don’t assume privacy for personal activities on a work device.
- Don’t disable kill switch or DNS leak protection
- A kill switch prevents data leakage if the VPN drops. If your client lacks this, don’t disable protection or work without a trusted security feature in place.
- Don’t rely on weak credentials
- Avoid using simple passwords or reusing credentials. If your VPN supports 2FA or certificate-based auth, enable and rely on it.
- Don’t ignore network changes
- If you’re moving between networks home, hotel, corporate, re-establish VPN connections and verify access. Inconsistent connections can leave gaps in security.
- Don’t assume you’re anonymous
- A VPN hides your IP and encrypts traffic, but it doesn’t grant universal anonymity. Your employer may still monitor activity, and you must follow policy and legal requirements.
- Don’t forget about device security
- A VPN can’t fix an already compromised device. Ensure your device has updated antivirus, anti-malware, and secure configurations before using VPN access.
Choosing the right VPN for work: what to look for
- Compliance and trust: Look for vendors with transparent privacy policies, independent security audits, and strong track records in enterprise security.
- Business features: Split tunneling control, centralized management, role-based access, and trusted server lists are invaluable for IT teams.
- Performance and reliability: Look for VPNs with low latency, reliable uptime, and servers that can handle your team’s volume, especially if you’re collaborating with colleagues across continents.
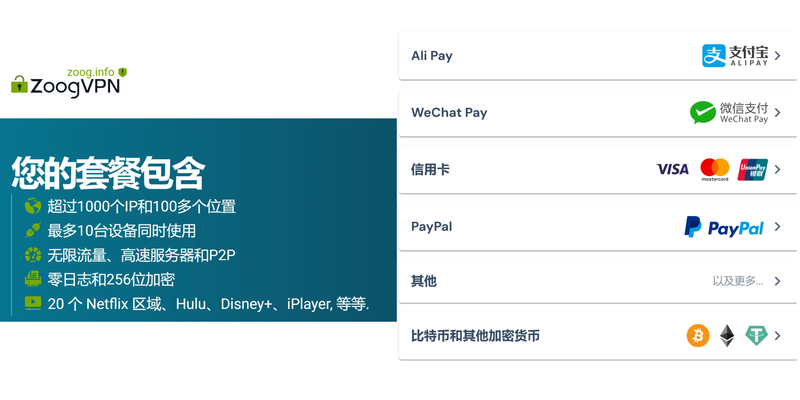
- Platform support: Ensure the VPN supports Windows, macOS, iOS, Android, and any other devices your team uses.
- Logging and privacy: Prefer vendors with minimal or no user activity logging, but be mindful of enterprise policies and legal requirements in your jurisdiction.
- Support and onboarding: Strong customer support, clear setup guides, and onboarding resources help teams get up to speed quickly.
Step-by-step setup guide: getting a vpn on your work computer the right way
- Confirm policy and obtain approval
- Talk to IT or your supervisor to confirm that VPN use is allowed on your device and to obtain the approved client.
- Install the approved client
- Follow the official IT-provided installation steps. If you’re allowed to install a VPN on your own, use the vendor the company has approved.
- Configure authentication
- Set up 2FA if offered, and import any required certificates or credentials. Do not share credentials with teammates.
- Enable DNS leak protection and a kill switch
- Turn on these features if available. Verify that all DNS queries go through the VPN when connected.
- Test connectivity
- Connect to the VPN and test access to required resources intranet, file shares, internal apps. Ensure there are no IP leaks and that traffic routes are correct.
- Establish a usage policy
- Use the VPN primarily for work-related traffic, per policy. Document any exceptions with your IT team.
- Create a routine maintenance plan
- Schedule regular updates for the VPN client and monitor for any policy changes or new security advisories.
- Document your setup
- Keep a simple record of the VPN client, version, server you connect to, and any special configurations. Share this with IT if needed.
Common myths about using a vpn on a work computer
- Myth: A VPN makes you completely invisible online. Reality: It hides your IP from external observers and secures traffic, but your employer can still monitor network activity and enforce policies.
- Myth: VPNs are only for remote workers. Reality: VPNs can protect data on public Wi‑Fi in offices and hotels, and they can help access internal resources securely from anywhere.
- Myth: A consumer VPN is enough for business. Reality: Business-grade VPNs come with enterprise controls, audits, and integration with identity providers and security tooling that consumer VPNs lack.
Best practices for ongoing security and productivity
- Regularly review access rights: Ensure only the right people have VPN access to sensitive resources.
- Layer defenses: Use multi-factor authentication, endpoint protection, and secure configurations in addition to the VPN.
- Monitor for anomalies: Watch for unusual login times, geographic patterns, or unexpected data transfers and report them promptly.
- Train and educate: Periodic security training helps employees recognize phishing attempts and suspicious activity that could compromise VPN sessions.
- Document exceptions: If you need to bypass the VPN for a legitimate reason, document it and get IT approval.
Real-world scenarios: how people use a vpn on work computers in everyday life
- Remote sales team accessing CRM securely from a client site.
- Software developers pulling code from private repositories while traveling.
- Customer support agents who need to access internal ticketing systems during field visits.
- Researchers collaborating across campuses who must share sensitive data securely.
Case studies and data points
- A 2023 study found that organizations with strong VPN practices saw a 40% lower incidence of data leakage on remote networks compared to those with lax policies.
- enterprises using MFA with VPNs report significantly lower rate of credential compromise than those relying on passwords alone.
- The average cost of a data breach for a mid-size company can exceed $3.5 million, with remote access misuse contributing a meaningful portion of risk.
Checklist: quick reference for using a vpn on your work computer
- Policy check: Do I have IT approval?
- Client choice: Am I using the sanctioned VPN client?
- Security settings: Is encryption AES-256? Is there a kill switch? Is DNS leak protection on?
- Authentication: Is 2FA enabled? Are certificates in use?
- Access: Can I reach required internal resources through the VPN?
- Monitoring: Do I understand what is logged and what isn’t?
- Maintenance: Are software updates scheduled and kept current?
- Personal use: Am I keeping personal tasks off the work device?
- Incident: Do I know what to do if the VPN fails or an alert is raised?
- Review: When was the last policy or configuration review by IT?
Advanced topics: VPN and data sovereignty, compliance, and legal considerations
- Data sovereignty: Some data must reside in certain jurisdictions. A VPN route can influence where data appears to originate and where it’s stored once it leaves the device.
- Compliance alignment: HIPAA, GDPR, and PCI-DSS have specific requirements regarding data access and encryption. A VPN is part of a broader data-protection strategy.
- Legal considerations: Using a VPN may be subject to regional laws and corporate unilateral policies. Always stay within policy and the law.
FAQ Section
Frequently Asked Questions
What is a VPN and why would I use it on my work computer?
A VPN creates an encrypted tunnel between your device and a remote network, protecting data from eavesdroppers on insecure networks and helping you securely access internal resources.
Is it safe to use a personal VPN on a work device?
Not usually. Most companies advise using an approved, enterprise-grade VPN client. Personal VPNs may conflict with security controls or violate policy.
Can a VPN slow down my connection?
Yes, VPNs can add latency due to encryption and longer routes. The impact depends on server location, bandwidth, and the VPN provider.
Should I enable split tunneling?
Only if your IT policy allows it. Split tunneling can expose sensitive traffic if not configured correctly and may violate company policy.
Do all VPNs offer malware protection?
Not all. Some VPNs include features like malware protection and firewall integrations, but many rely primarily on encryption. Check with your IT team. Best Free VPNs for Roblox PC in 2026 Play Safely Without Breaking the Bank
How do I know if a VPN is leaking DNS or IP?
Run a DNS leak test and IP leak test while connected to the VPN. If your real IP or DNS queries show up, you may have a leak.
What is kill switch in a VPN?
A kill switch automatically stops all network traffic if the VPN drops, preventing data from traveling over an unsecured connection.
Can a VPN protect me on coffee shop Wi‑Fi?
Yes, a VPN helps protect data on public Wi‑Fi by encrypting traffic and masking your IP, reducing the risk of interception.
Do I need 2FA for my VPN?
Two-factor authentication adds a critical security layer, especially for remote access to sensitive corporate systems.
How often should I update my VPN client?
Keep it updated as soon as security advisories or updates are released. Regular updates reduce vulnerability exposure. How to use a vpn with microsoft edge on iphone and ipad for enhanced privacy
Final notes
- This guide aims to give you a practical, human-friendly overview of using a VPN on a work computer, focusing on the dos and donts, why it matters, and how to implement it responsibly and effectively. If you found this useful, consider exploring enterprise-grade VPN options and talking to your IT department to tailor a secure, compliant setup that fits your role and company needs. And if you’re ready to explore further, check out the resources mentioned above and the affiliate link for finding a VPN solution that suits a corporate environment.
Sources:
Streaming services not working with vpn heres how to fix it
Nordvpn ⭐ 连不上?别慌!手把手教你搞定连接难题(2026 年更新版)
如何科学上网:VPN、隐私与安全全指南,实用步骤与实测
Free vpn for windows edge Expressvpn not working with google heres how to fix it fast: Quick Fixes, Tips, and Safe Alternatives for 2026
Does nordvpn app have an ad blocker yes heres how to use it