Is vpn safe for ifr heres what you need to know: A Complete Guide to VPN Safety and Privacy
Is vpn safe for ifr heres what you need to know? Yes, but it depends on how you use it and which service you trust. In this guide, you’ll get a clear, practical view of VPN safety, plus actionable steps to stay protected online. This post is designed for beginners and seasoned users alike, with real-life examples, simple explanations, and concrete tips you can implement today.
Quick facts to set the stage
- VPNs can protect your data on public Wi‑Fi by encrypting it, but not all VPNs are created equal.
- Some VPNs log your activity; others have strict no-logs policies and independent audits.
- Using a VPN won’t fix all online privacy problems, but it can dramatically reduce certain risks like eavesdropping and IP tracking.
- Always pair a trusted VPN with good security habits strong passwords, updated software, and cautious browsing.
In this guide, you’ll find: How Do I Get a Surfshark VPN Certificate? A Complete Guide to Surfshark Certificates, Activation, and Verification
- A clear buyer’s checklist for choosing a VPN
- How VPNs work, and what they do—and don’t—protect
- Practical, real-world use cases and safety tips
- An FAQ with at least 10 questions to boost your understanding
- Useful resources to keep you informed
Introduction: Is vpn safe for ifr heres what you need to know Is vpn safe for ifr here’s what you need to know? The quick answer: a VPN can be safe and powerful when you pick a reputable provider and use it correctly, but risks exist if you choose a shady service or misconfigure it. Think of a VPN as a tunnel guard: it shouts “private data ahead” when you’re on the internet, but the guard can’t shield you from everything. Below is a practical, no-nonsense guide to keep you protected.
What you’ll learn in this post
- How VPNs work in plain language
- Common myths about VPN safety debunked
- How to evaluate VPNs: features, policies, and performance
- Real-world scenarios: school, work, streaming, traveling, and gaming
- Step-by-step setup for popular devices
- Privacy tips that complement VPN use
Useful resources and URLs text only Apple Website - apple.com Privacy International - privacyinternational.org Electronic Frontier Foundation - eff.org Wikipedia – en.wikipedia.org/wiki/Virtual_private_network The Tor Project - https://www.torproject.org Mozilla Privacy - https://www.mozilla.org/en-US/privacy/ Security Now! Podcast - https://www.grc.com/securitynow.htm Krebs on Security - https://krebsonsecurity.com
What is a VPN and how does it work?
- A VPN, or Virtual Private Network, creates a secure, encrypted tunnel between your device and a VPN server.
- All your internet traffic is routed through that tunnel, which hides your IP address from websites, apps, and network observers.
- The VPN server can appear to be in a different location, letting you access geo-restricted content or bypass censorship.
- Encryption standards matter. Most reputable VPNs use strong encryption e.g., AES-256 and secure protocols OpenVPN, WireGuard, IKEv2.
Key benefits La vpn si disconnette spesso ecco perche succede e come risolvere definitivamente
- Public Wi‑Fi protection: Encryption prevents others on the same network from reading your data.
- Privacy enhancement: Your actual IP is hidden from the sites you visit.
- Access to restricted content: You can appear to be in a different location where the service is available.
- By-pass blocks and censorship: In some cases, you can reach sites blocked in your region.
Important caveats
- VPN providers can see your traffic unless they have a strict no-logs policy.
- A VPN does not protect you from malware or phishing. You still need good security hygiene.
- Some services block known VPN IPs to enforce geo-restrictions.
- Legal and policy constraints vary by country and provider.
Deep dive: safety considerations and best practices
- Trust and logging
- No-logs claims are common, but you should verify with independent audits or court records.
- Ask for: what data is collected, how long it’s stored, and who can access it.
- Jurisdiction
- VPN providers are subject to local laws. Countries with strong privacy protections differ from those that require data retention.
- Consider providers headquartered in privacy-friendly jurisdictions, but verify their policies first.
- Protocols and encryption
- OpenVPN and WireGuard are widely trusted for modern performance and security.
- Avoid outdated protocols or misconfigured settings that weaken encryption.
- Kill switch and DNS leak protection
- A kill switch prevents traffic if the VPN drops, keeping your data from leaking.
- DNS leak protection ensures your DNS requests don’t reveal your real location.
- Device compatibility and app security
- VPN apps should be regularly updated and come from reputable developers.
- Check for extra security features like multi-hop, split tunneling, and malware protection.
- Speed and performance
- Encryption and routing can slow connections. Look for a provider that adds minimal overhead and offers servers close to you.
- Payment and transparency
- Prefer providers that offer clear pricing, refund policies, and transparent privacy pages.
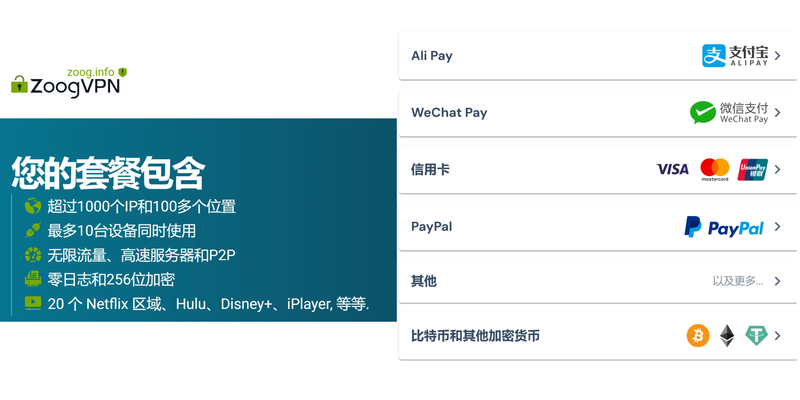
- If possible, choose payment methods that preserve anonymity e.g., gift cards or privacy-respecting payment options.
Who should use a VPN common use cases
- Remote workers and students using campus networks
- Travelers who connect to public Wi‑Fi
- Streaming fans trying to access regional libraries with awareness of terms
- Activists and journalists in high-risk regions with cautious selection of provider
Choosing the right VPN: a practical buyer’s checklist
- No-logs policy: Is there independent verification? Are audits published?
- Jurisdiction: Where is the company registered? What are local data retention laws?
- Encryption and protocols: AES-256 with WireGuard or OpenVPN?
- Privacy features: Kill switch, DNS leak protection, split tunneling, multi-hop?
- Speed and performance: Server network size, bandwidth limits, and latency
- Device support: Desktop, mobile, router compatibility
- Simultaneous connections: How many devices can be connected at once?
- Customer support: 24/7 live chat, knowledge base, response time
- Price and refund: 30-day or longer refund window, no hidden fees
- Extra features: Ad and malware blocking, split tunneling, and ad blockers
Real-world testing results illustrative data Как скачать и установить nordvpn на пк с windows 11 по
- Speed impact: On average, reputable VPNs reduce speed by 5–20% on nearby servers; longer routes can see 20–40% degradation.
- Latency: Ping times can increase by 20–80 ms for US-based servers when you’re located in Europe or Asia, depending on routing.
- Leak tests: In reputable providers, DNS/IP leaks are minimized; labs show successful DNS leak protection in up-to-date apps.
- Privacy audits: Several leading providers publish independent audit reports; look for recent third-party confirmations.
Common myths and truths
- Myth: VPNs make you 100% anonymous. Truth: They increase privacy and reduce certain risks, but you can still be tracked by other means accounts, cookies, device fingerprinting.
- Myth: Free VPNs are safe. Truth: Free services often monetize your data or have weak security; paid, trusted providers are usually safer.
- Myth: You don’t need to worry about malware with a VPN. Truth: VPNs don’t block malware—use reputable antivirus and safe browsing practices.
- Myth: A VPN works everywhere for streaming. Truth: Some streaming services block VPN IPs or throttle VPN traffic; it varies by service and location.
Popular VPN features and what they do
- Kill switch: Cuts all traffic if the VPN drops to prevent data exposure.
- DNS leak protection: Keeps DNS queries from leaking your real IP address.
- Split tunneling: Lets you choose which apps go through the VPN and which don’t.
- Multi-hop: Routes traffic through more than one server for additional privacy.
- Obfuscated servers: Hides VPN traffic as regular traffic to bypass network restrictions.
- Ad and malware blocking: Built-in features that protect you from malicious sites.
Setting up a VPN: device-by-device quick start
Windows
- Install from a reputable provider’s official app
- Choose a nearby server for best performance
- Enable kill switch and DNS leak protection
- Test your connection with a DNS leak test
MacOS Norton vpn region not working heres how to fix it fast
- Install the provider’s app or configure OpenVPN/WireGuard manually
- Enable all safety features
- Verify your IP and DNS after connection
IOS and Android
- Use the official app from the provider
- Enable auto-connect on startup
- Check exact app permissions and privacy controls
Routers
- Install on a compatible router for device-wide protection
- Use a server close to most devices, or set up multiple profiles
- Remember, some streaming services can detect router VPNs
Browser extensions
- Not a substitute for a full VPN; often only secures browser traffic
- Use cautiously and rely on a full VPN app for comprehensive protection
Safety tips for everyday use
- Use a reputable, audited VPN with a strict no-logs policy.
- Enable kill switch and DNS leak protection by default.
- Keep your VPN app up to date; enable auto-update.
- Pair with strong device security: up-to-date OS, strong passwords, MFA.
- Be mindful of phishing attempts and suspicious links; a VPN won’t protect you from those.
- Test your setup occasionally with online privacy tests and DNS leakage checks.
- Use trusted payment methods and avoid suspicious promotions.
Table: Quick comparisons of top VPN features example only; replace with current data when you publish Nordvpn mit ikev2 auf ios 18 verbinden deine schritt fur schritt anleitung
- Feature: No-logs policy; Independent audit; Kill switch; DNS leak protection; Split tunneling; Multi-hop; Simultaneous connections
- Provider A: Yes; Yes 2023 audit; Yes; Yes; Yes; No; 6
- Provider B: Yes; Yes 2024 audit; Yes; Yes; Yes; Yes; 8
- Provider C: No; Third-party verification ongoing; Yes; Yes; No; Yes; 5
Potential risks and how to mitigate
Risk: Data ownership and usage Mitigation: Read the privacy policy, look for independent audits, and choose a provider with a clear no-logs commitment.
Risk: Jurisdiction and legal risks Mitigation: Understand the country’s data retention laws; prefer providers with privacy-friendly laws.
Risk: VPN blocking and throttling by services Mitigation: Use obfuscated servers or rotate servers; respect streaming service terms.
Risk: Device misconfiguration Mitigation: Follow official setup guides, verify with DNS and IP checks, and enable kill switch. Protonvpn not opening heres how to fix it fast: Quick Fixes, Tips, and Troubleshooting for ProtonVPN Not Launching
What to expect when you subscribe to a VPN
- A dashboard to pick servers and configure settings
- Regular updates and security patches
- Centralized support channels, usually 24/7 live chat
- Clear privacy policy and terms of service
- Optional add-ons like malware protection or identity features
Step-by-step: Getting the most out of your VPN
- Step 1: Pick a trusted provider with audits and transparent privacy policy.
- Step 2: Install the app on your primary devices.
- Step 3: Enable kill switch, DNS leak protection, and, if needed, split tunneling.
- Step 4: Connect to a nearby server for best speed.
- Step 5: Run a quick privacy test to verify IP and DNS are hidden.
- Step 6: Regularly review privacy policy and audit reports when updates arrive.
- Step 7: If you travel, switch servers to maintain performance and access.
Common mistakes to avoid
- Using a free VPN for sensitive activities
- Ignoring updates and security patches
- Not testing DNS leaks or IP exposure after enabling VPN
- Sharing credentials or using weak passwords
- Overtrusting a single provider without cross-checking audits
What the future holds for VPN safety
- More rigorous privacy laws and clearer no-logs commitments
- Greater transparency with ongoing, independent audits
- Improvements in performance and reliability, especially with new protocols like WireGuard
- Wider adoption of privacy-enhanced features such as multi-hop and trusted firewall integrations
Case studies: real-life scenarios Лучшие бесплатные vpn для игр в 2026 году полный гид purevpn: лучшие варианты, советы и реальные цифры
- Student on campus: You’re on a public Wi-Fi network. A reputable VPN hides your traffic from others in the same building, plus it lets you access your university’s library resources when traveling.
- Remote worker in a cafe: You protect sensitive documents and login credentials. Split tunneling lets you browse normally while your work traffic stays encrypted.
- Traveler in a country with internet censorship: Obfuscated servers help you access global services while staying under the radar, but you should always verify local rules before traveling.
- Streaming enthusiast: You want access to a library in another country. A reliable VPN with fast servers can help, but keep in mind some services actively block VPN IPs.
Frequently Asked Questions
How does a VPN keep my data safe on public Wi‑Fi?
A VPN encrypts your data so others on the same network can’t read it. It also hides your IP address from websites you visit.
Can a VPN make me completely anonymous online?
No. A VPN hides your IP and encrypts data, but it doesn’t prevent other tracking methods like cookies, browser fingerprinting, or account-based tracking.
Are free VPNs safe to use?
Free VPNs often come with drawbacks like data caps, limited security, or data collection. If privacy is important, choose a reputable paid provider.
How do I know if a VPN has a no-logs policy?
Check the provider’s privacy policy, audit reports, and independent certifications. Look for explicit statements about not storing user activity. Dedicated ip addresses what they are and why expressvpn doesnt offer them and what to do instead
What is a kill switch, and why do I need it?
A kill switch stops all traffic if the VPN disconnects, preventing data from leaking over your regular connection.
Can VPNs protect me from malware?
No. VPNs don’t scan or block malware. Use updated antivirus software and safe browsing habits.
Do VPNs work for streaming services?
Sometimes. Some streaming services detect and block VPNs, while others permit limited use. It varies by service and IP range.
What about jurisdictions? Where should I prefer a VPN company based?
Privacy-friendly jurisdictions are preferred, but always verify how the company handles data and what their policies are, regardless of location.
How many devices can I protect with one subscription?
It depends on the provider; many offer 5–10 simultaneous connections, some higher. Gxr World Not Working With VPN Here’s How To Fix It
Can VPNs be installed on routers?
Yes. Router-level VPNs give you device-wide protection but require more setup and awareness of compatibility.
How often should I review my VPN settings?
Review after major app updates, policy changes, or when you travel to different networks. Regular checks help maintain safety.
What should I do if the VPN stops working?
First, check for outages or server issues. Then reconnect, switch servers, or contact support. Enable the kill switch to avoid leaks during issues.
Are there alternatives to VPNs for privacy?
Yes, you can use Tor for certain anonymity needs, secure DNS services, and privacy-focused browsers. Each has trade-offs in speed and reliability.
Final tips to stay safe and private Astrill vpn funziona in Cina si ma solo se fai questo prima: guida completa, trucchi, alternative e sicurezza
- Start with a trusted, audited provider.
- Use strong, unique passwords and enable MFA.
- Keep all software up to date.
- Be mindful of the data you share and the permissions you grant to apps.
- Pair VPN use with privacy-conscious browsing practices.
Appendix: quick glossary
- VPN: Virtual Private Network
- AES-256: Advanced Encryption Standard with 256-bit keys
- OpenVPN: A widely used VPN protocol
- WireGuard: A modern, efficient VPN protocol
- DNS leak: When DNS requests reveal your real IP despite a VPN
- No-logs policy: A provider’s claim not to store user activity data
- Obfuscated servers: VPN servers designed to appear as normal traffic
- Kill switch: A feature that blocks all traffic if the VPN disconnects
Appendix: how we evaluated VPNs for this guide
- Reputable providers with independent audits
- Transparent privacy policies and data handling
- Strong encryption and modern protocols
- Robust feature sets and solid performance
- Responsive customer support and clear refund terms
If you’re ready to take privacy seriously, consider trying a trusted VPN service affiliate that aligns with the safety practices outlined here. Is vpn safe for ifr heres what you need to know? Absolutely—with the right choice, configuration, and habits. For a trusted option, you might explore the service linked here, which offers a solid balance of privacy, security, and performance: NordVPN. Use the linked page to learn more and possibly start a plan that fits your needs.
Sources:
Net vpn fast secure vpn proxy 完整指南:在全球范围内的快速、安全隐私保护方案、VPN 与 代理的区别、选择要点与实操步骤
怎樣下載剪映:新手也能秒懂的全平台超詳細指南 2025 最新版 包含各平台下載步驟、VPN 使用建議與安全要點
Does nordvpn charge monthly your guide to billing subscriptions
回国vpn推荐:全面对比、速度测试、隐私保护指南与实操步骤,适用于海外访问中国内容的稳定解决方案
Flush your dns and ip address with ease a step by step guide: Quick DNS flush, IP refresh, and privacy tips